In the introduction, Engels gives an example of how we can can judge the cost of labour. He states
Let us assume that the money price of these means of subsistence [the cost to keep the labourer able and willing to work] averages 3 shillings a day. Our laborer gets, therefore, a daily wage of 3 shillings from his employer. For this, the capitalist lets [makes] him work, say, 12 hours a day. Our capitalist, moreover, calculates somewhat in the following fashion: Let us assume that our laborer (a machinist) has to make a part of a machine which he finishes in one day. The raw material (iron and brass in the necessary prepared form) costs 20 shillings. The consumption of coal by the steam-engine, the wear-and-tear of this engine itself, of the turning-lathe, and of the other tools with which our laborer works, represent, for one day and one laborer, a value of 1 shilling. The wages for one day are, according to our assumption, 3 shillings. This makes a total of 24 shillings for our piece of a machine.
But, the capitalist calculates that, on an average, he will receive for it a price of 27 shillings from his customers, or 3 shillings over and above his outlay.
Whence do they 3 shillings pocketed by the capitalist come? According to the assertion of classical political economy, commodities are in the long run sold at their values, that is, they are sold at prices which correspond to the necessary quantities of labor contained in them. The average price of our part of a machine – 27 shillings – would therefore equal its value, i.e., equal the amount of labor embodied in it. But, of these 27 shillings, 21 shillings were values were values already existing before the machinist began to work; 20 shillings were contained in the raw material, 1 shilling in the fuel consumed during the work and in the machines and tools used in the process and reduced in their efficiency to the value of this amount. There remains 6 shillings, which have been added to the value of the raw material. But, according to the supposition of our economists, themselves, these 6 shillings can arise only from the labor added to the raw material by the laborer. His 12 hours’ labor has created, according to this, a new value of 6 shillings. Therefore, the value of his 12 hours’ labor would be equivalent to 6 shillings. So we have at last discovered what the “value of labor” is.
“Hold on there!” cries our machinist. “Six shillings? But I have received only 3 shillings! My capitalist swears high and day that the value of my 12 hours’ labor is no more than 3 shillings, and if I were to demand 6, he’d laugh at me. What kind of a story is that?"
If before this we got with our value of labor into a vicious circle, we now surely have driven straight into an insoluble contradiction. We searched for the value of labor, and we found more than we can use. For the laborer, the value of the 12 hours’ labor is 3 shillings; for the capitalist, it is 6 shillings, of which he pays the workingman 3 shillings as wages, and pockets the remaining 3 shilling himself. According to this, labor has not one but two values, and, moreover, two very different values!
As soon as we reduce the values, now expressed in money, to labor-time, the contradiction becomes even more absurd. By the 12 hours’ labor, a new value of 6 shillings is created. Therefore, in 6 hours, the new value created equals 3 shilling – the amount which the laborer receives for 12 hours’ labor. For 12 hours’ labor, the workingman receives, as an equivalent, the product of 6 hours’ labor. We are, thus, forced to one of two conclusions: either labor has two values, one of which is twice as large as the other, or 12 equals 6!This binary conclusion that Engels presents is the basic flaw of Marx and Engel's theories; when a customer is buying a part from the Capitalist, the customer is not simply buying the part, but she is also purchasing the service of simplifying the acquisition of said part. The Capitalist adds value to the "experience" of purchasing the part for the customer. Without the intervention of the Capitalist, the Customer would need to perform many tasks to obtain the needed part. The Customer would need to obtain access to the machinery, vet and chose potential labourers, calculate the cost of subsistence for the labourers, and transport the finished part to where it is needed. By handling these tasks, the Capitalist can justify adding his 3 shillings to the cost of the part.
Engels does not seem to understand that when a customer buys a thing, she not only buys the thing, but also buys the service involved in getting the thing to her. Thus we can now understand that there is not one single labour cost but two costs of labour added to the raw materials and deprecation value of tools. There is a "production labour" and a "service labour."
Simply put there are not two values of labour... there are two labours, each with value. Engels is wrong when he states "the working class alone produces all values." While it is true that the working class alone produces all _production_ values, the working class produces nearly none of the service values.
Even if the bourgeois Capitalist were to employ someone to manage the service labour involved in selling the part (we will call these labourers "managers"), there is still a labour associated to maintaining the management or a risk involved in neglecting them; for if the Capitalist owner does not oversee management, their business is at greater risk of failure.































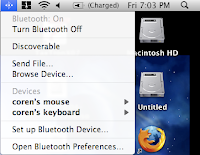
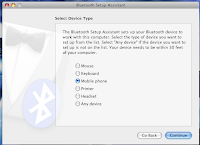
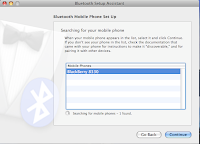
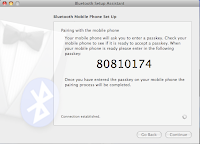
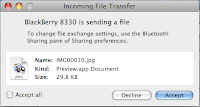
 ck* -> BlackBerry 8330 Continue *click* -> Continue *click* -> Remember NUMBERS
ck* -> BlackBerry 8330 Continue *click* -> Continue *click* -> Remember NUMBERS